It's Unbelievable How Something as innocuous as a USB Drive can destroy your Computer! - Robotics, Technology & Cyber Security

Mechanical Keyboard Attack Shark K98 Luminous USB Wired hot-swapable mechanical keyboard Customization gaming esports keyboard - AliExpress

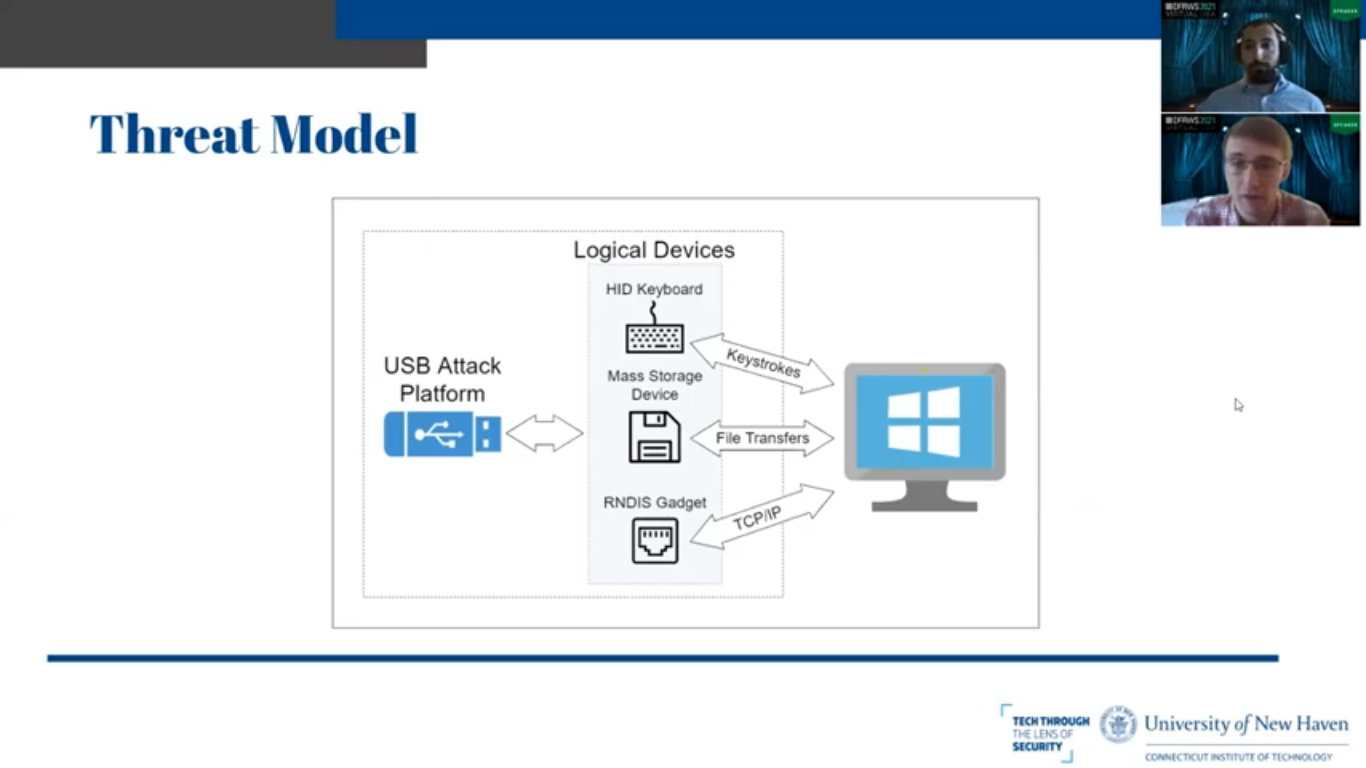
HID Attack. The external device can inject input events. The malicious... | Download Scientific Diagram
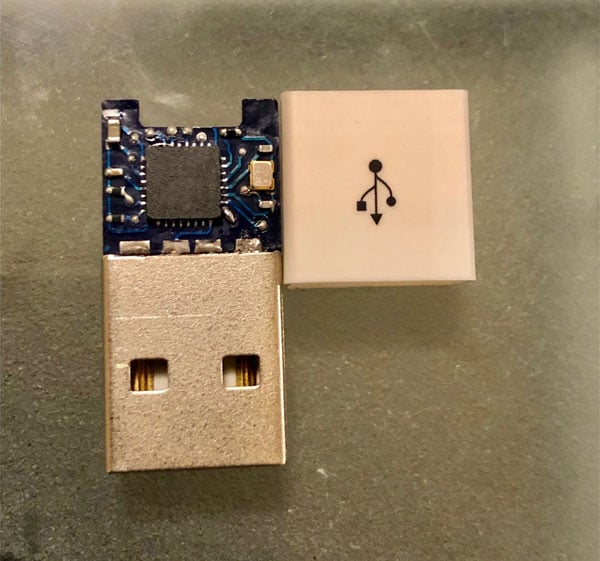
GitHub - samyk/usbdriveby: USBdriveby exploits the trust of USB devices by emulating an HID keyboard and mouse, installing a cross-platform firewall-evading backdoor, and rerouting DNS within seconds of plugging it in.

USB HID Attacks. USB HID devices are the way we interact… | by evildaemond | Heck the Packet | Medium

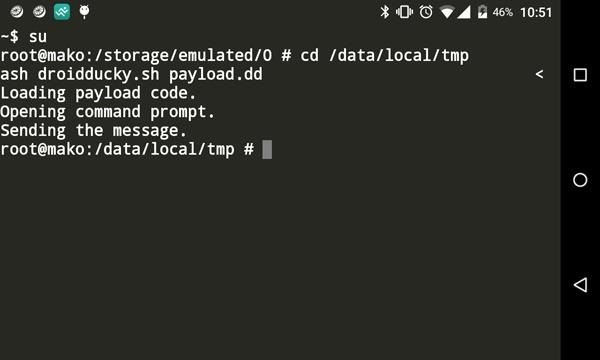
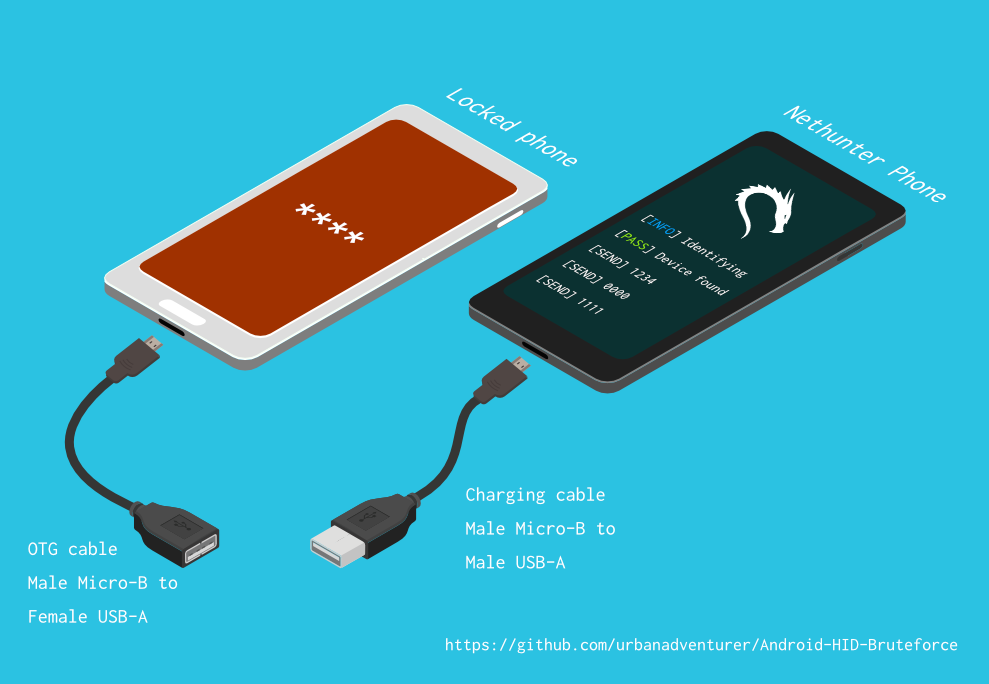
NetHunter Hacker VI: Ultimate guide to HID attacks using Rubber Ducky scripts and Bad USB MITM attack - Mobile Hacker

Mechanical Keyboard Attack Shark K98 Luminous USB Wired hot-swapable mechanical keyboard Customization gaming esports keyboard - AliExpress
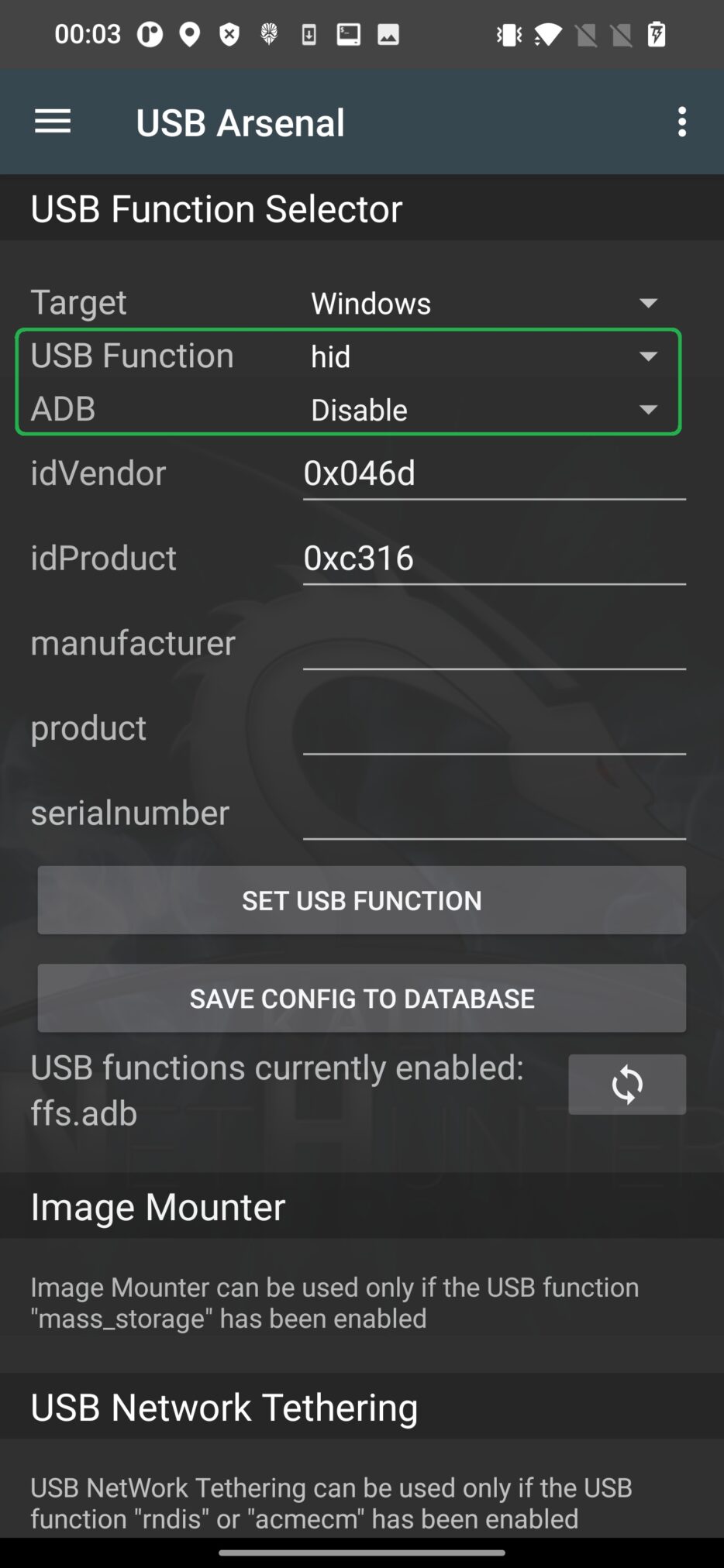
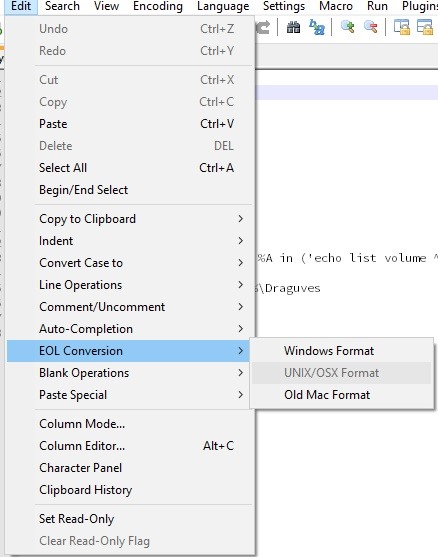
NetHunter Hacker VI: Ultimate guide to HID attacks using Rubber Ducky scripts and Bad USB MITM attack - Mobile Hacker

It's Unbelievable How Something as innocuous as a USB Drive can destroy your Computer! - Robotics, Technology & Cyber Security